Bluetooth tracking devices/tags/”key” finders
A while ago in coverity while fixing FFmpeg bugs there was a some kind of Nominate a bug, win a prize thing, i didnt ever nominate one but this was when i learned about the existence of tile which would have been the prize one could win. A BLE device that can be attached to something valuable and that can then be searched and found with a recent android or iPhone, or the other way around using the device to find your phone.
This seemed potentially useful to me, though i personally have never lost my keys or phone for more than a few seconds, i know someone who does have that problem. So i thought buy a tile or 2 they might come in handy for something but then i saw the price, non replaceable, non rechargable battery and thought ok, didnt expect someone would be that lame. I guess one should not expect any company not to attempt to rip its customers off to the maximum extend possible.
Lucky there are many similar devices, so the goal was to find the cheapest that works and is not just tied to a ridiculous business model. So i bought some of the cheapest i could find (they of course all have user replaceable batteries …)
First is something that identifies itself as
ITAG
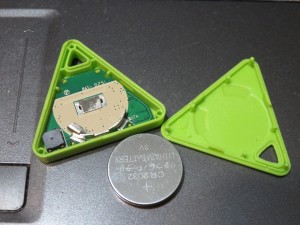

The above one is one example of these, they come in many different shapes, cost less than 5$ with free shipping. The first i got had a different shape and came with a dead battery and also ate a new battery within a day. The second i got is the one pictured above, which worked more or less.
When Off, A long press on its large surface switches it on with 2 beeps.
When On or connected a long press switches it off with a long beep (this renders it useless as its easy to press by mistake)
When on but not connected its led also continuously blinks, draining the battery but making finding easier, it also at least once hanged and required the battery to be disconnected for a moment to function again.
On the BT protocol side setting immedeate alert to 2 results in 30 beeps and led blinks, setting link loss to 0 or 2 has no effect, the device always beeps on unintentional connection losses as far as i could figure out. pressing the button results in a notify with value 0x01 on 0000ffe0-0000-1000-8000-00805f9b34fb / 0000ffe1-0000-1000-8000-00805f9b34fb.
To make the itag only blink and not beep on immedeate alert, 0000fff0-0000-1000-8000-00805f9b34fb/0000fff1-0000-1000-8000-00805f9b34fb can be set to 0x00, this is remembered over disconnects but not over switching the tag off. All other values seem to cause blinking and beeping.
To identify it this may be helpfull:
- 0x2A29: CEVA
- 0x2A24: BT 4.0
- 0x2A25: 12x07x2012
- 0x2A27: SM-1
- 0x2A50: Bluetooth SIG Company: Ceva, Inc. (formerly Parthus Technologies, Inc.)
Product Id:13330
Product Version: 26369
Smart Finder


The above is another sub 5$ tag, which appears identical (minus the logos) to tags on amazon from chirotronix and ikee.
The official software for android (“small lovely”) has a rather long list of unneeded permissions like for the previous tag (“iTracing”) but for this theres also no inofficial sw i could find for android which supports these tags, which is why i reverse engeneered the protocol
When off a long press switches it on with a long beep, to switch it off again 5 rapid short presses are needed (resulting in 3 beeps).
When in On mode pressing the button results in 2 beeps this also causes the “#255 Manufacturer Specific Data” to change from 0x58,0x48,0x52 to 0x58,0x48,0xFF for a few seconds, apparently to identify which of potential several devices one wants to connect to. Switching the device off also seems not possible while it is connected. On connect and disconnect its led flashes once.
Protocol wise neither “link loss” nor “immedeate alert” have any effect that i could identify. To make the device beep and blink a command must be written to 0000fff0-0000-1000-8000-00805f9b34fb / 0000fff1-0000-1000-8000-00805f9b34fb. A single 0xAA results in some short beeps and blinking. Its also possible to write a 5 byte command 0xAA 0x03 count duration1 duration2. The count is the number of beeps, the 2 durations are the beep and non beep durations in milli seconds, i dont know what the 0x03 does or if there are other interesting commands.
To detect button presses the device can send notifies on 0000fff0-0000-1000-8000-00805f9b34fb / 0000fff1-0000-1000-8000-00805f9b34fb with a 3 byte value, it is either (0x01 xx 0x00) xx = number of short button presses or (0x02 0x00 xx) xx = number of seconds button is hold
To identify it this may be helpfull:
- 0x2A29: SIGNAL
- 0x2A24: BT A8105
- 0x2A25: 00001
- 0x2A26: F4F5V02
- 0x2A27: A8105F4
- 0x2A28: 1030627
The name of teh device is “AMIYJ_5B68”, i dont know if this is true for all these devices, google seemed not to have any hits on that.
It seems using a A8105, (the ITAG seems using a BK3431) datasheets can be found with google.
Interestingly theres also a entry for “Heart rate” on the bluetooth level, so i guess this shares some code with some other devices.
Hope something above is useful to someone
Update: 2015-11-09: corrected itags link loss behavior
Update: 2015-11-10: Added names of the official apps
Update: 2015-11-14: Added itag blink only info (found by and thanks to Joachim Schäfer)





































